https://twitter.com/CISAgov/status/1319372231647035392Russian state-sponsored cyber actor has targeted dozens of U.S. governments & aviation sector networks.
CERT-i kokkuvõte
https://us-cert.cisa.gov/ncas/alerts/aa20-296a
https://twitter.com/CISAgov/status/1319372231647035392Russian state-sponsored cyber actor has targeted dozens of U.S. governments & aviation sector networks.
https://twitter.com/uuallan/status/1321477875648942086Another hospital hit with ransomware...that is at least 5 (in the US) in the last 24 hours. Still looking for more.
https://twitter.com/thenamecast/status/ ... 4295761920Ryuk operated bu WIZARD SPIDER out of Russian. Russian cybercriminals operate either under the permission or direction of the Kremlin.
If true, this is an unthinkable act of war. Targeting hospitals is inhuman.
https://twitter.com/akihheikkinen/statu ... 6821273605Officials Warn of Cyberattacks on Hospitals as Virus Cases Spike
"Hundreds of American hospitals are being targeted in cyberattacks by the same Russian hackers"
https://twitter.com/briankrebs/status/1 ... 0474331136On Monday, KrebsOnSecurity began following up on info provided by @holdsecurity that a ransomware group (Ryuk) is preparing to encrypt systems at possibly hundreds of medical centers/hospitals. FBI/CISA/HHS just had a call warning of "imminent, credible threat to US hospitals."
https://thehill.com/policy/cybersecurit ... cases-riseHospitals and health care institutions preparing for a fall wave of coronavirus cases are bracing for more cyberattacks after hackers seeking to take advantage of the pandemic launched several successful attacks this year that severely disrupted patient services.
Experts particularly warn about attacks involving ransomware viruses, which have become an increasing headache for governments and private sector groups. Ransomware involves an attacker gaining access to a system, encrypting it and preventing access, then demanding payment to restore the system.
According to Pienaar, some hospitals have opted to pay hackers in order to more quickly restore critical services during the pandemic, which experts say only emboldens criminals to use the tactic.
“Ransomware will continue to be a sectoral nuisance,” Greg Singleton, the director of HHS’s Health Sector Cybersecurity Coordination Center, said during a virtual appearance at CyberScoop’s CyberTalks conference on Friday.
“As long as they are being able to monetize it, as long as facilities are paying the ransom, actors will continue to go after it, so I expect moving forward, it’s really troubling and unfortunate, but we will see the ransomware continue on.”
Still, hospitals and health care groups themselves are far more zeroed in on the threats posed by hackers than before the pandemic, and overall efforts to address threats have increased significantly.
In the U.S., groups including the Department of the Homeland Security’s Cybersecurity and Infrastructure Security Agency, the FBI and the nonprofit Health Information Sharing and Analysis Center have mobilized to defend the health care sector, helping prevent potentially much graver attacks.
https://www.zdnet.com/article/us-cyber- ... an-malwareUS Cyber Command has exposed eight new malware samples that were developed and deployed by Russian hackers in recent attacks.
Six of the eight samples are for the ComRAT malware (used by the Turla hacking group), while the other two are samples for the Zebrocy malware (used by the APT28 hacking group).
Both ComRAT and Zebrocy are malware families that have been used by Russia hacking groups for years, with ComRAT being deployed in attacks for more than a decade, having evolved from the old Agent.BTZ malware.
Both Turla and APT28 have consistently updated both tools to add evasion techniques and keep their malware undetected.
The purpose of this recent US government exposé is to share recent versions of these hacking tools with the general public so system administrators and other defenders can add detection rules and update protective measures.
On Thursday, US Cyber Command's Cyber National Mission Force (CNMF) uploaded samples of the new ComRAT and Zebrocy versions on its VirusTotal account, while the Cybersecurity and Infrastructure Security Agency (CISA), in cooperation with the Federal Bureau of Investigation's CyWatch, published two security advisories describing ComRAT and Zebrocy's inner workings.
Malware strains formally linked to Russia for the first time
As Slovak cyber-security firm ESET pointed out this week, the joint CYBERCOM, CISA, and FBI alerts also mark the first time that ComRAT and Zebrocy have been formally linked to the Russian government's cyber-espionage units.
Attribution for both ComRAT and Zebrocy has always been done in an informal manner in reports published by privately-owned security vendors, but never in advisories published by government agencies.
The US government has not linked any of these recent samples to any recent security incidents.
In the past, ComRAT has been used to target ministries of foreign affairs and a national parliament (per ESET), while Zebrocy was used to target embassies and ministries of foreign affairs (also, per ESET).
Victims of both malware have been identified in Eastern Europe and Central Asia, US Cyber Command said.
Earlier this week, cyber-security vendor Accenture also published a report on recent Turla operations and its prevalence to use the ComRAT malware.
The joint US government advisory was published on Halloween. US cyber-security agencies have recently made it a habit to expose malware operations on well-known holidays as a way to send greetings to foreign threat actors.
See pole esimene kord, umbes 7a tagasi oli haiglatel sama jama.ruger kirjutas:USA-s käib mingi haiglate vastane küberrünnak, kus krüpteeritakse infosüsteeme. Viimase 24 tunni jooksul vähemalt 5 haiglat pihta saanud.https://twitter.com/uuallan/status/1321477875648942086Another hospital hit with ransomware...that is at least 5 (in the US) in the last 24 hours. Still looking for more.
https://www.bbc.com/news/technology-55165552The international vaccine supply chain has been targeted by cyber-espionage, according to IBM.
The company says it tracked a campaign aimed at the delivery "cold chain" used to keep vaccines at the right temperature during transportation.
The attackers' identity is unclear - but IBM said the sophistication of their methods indicated a nation state.
https://www.postimees.ee/7124986/eesti- ... eratsiooniEesti ja Ameerika Ühendriikide küberväejuhatused (Cyber Command) viisid septembrist novembrini läbi ühise küberoperatsiooni Eesti kaitseväe võrgus.
Operatsiooni eesmärgiks oli takistada pahatahtlike osapoolte sissepääsu võrku ning tugevdada mõlema riigi vahelist koostööd ja küberkaitse-alaseid võimeid, teatas kaitseministeerium.
«Ühised operatsioonid meie lähima liitlase USAga on vajalikud, et tagada meie teenuste küberturvalisus. Sellised operatsioonid annavad meie spetsialistidele võimaluse jagada kogemusi ning samuti võimaldavad saada tagasisidet meie praeguse küberkaitsevõime kohta. Operatsioon oli edukas verstapost meie kahepoolses koostöös USA partneritega,» ütles Eesti kaitseväe küberväejuhatuse ülema asetäitja Mihkel Tikk.
USA küberspetsialistid, keda nimetatakse Hunt Forward meeskonnaks ja Eesti küberväejuhatuse spetsialistid otsisid pahatahtlikke osapooli erinevates võrkudes ja platvormidel. USA on varasemalt läbi viinud sarnaseid operatsioone Euroopas koos teiste riikidega, ent tegemist oli esmakordse ühisoperatsiooniga Eesti ja USA küberekspertide vahel.
«Vaatamata pandeemiale, saame tegutseda Eestis ja mujal Euroopas, mis annab meile võimaluse õppida vastaste kohta, kes võivad ohustada ka Ameerika Ühendriike,» ütles brigaadikindral Joe Hartman, kes juhib Ameerika kübermissioonide keskust (Cyber National Mission Force).
Hartman märkis, et kübermeeskonnad otsivad, tuvastavad indikaatoreid ja eemaldavad aktiivselt vastaspoolte pahavara. «Seejärel jagame teavet selle pahavara kohta, mitte ainult USA valitsusega, aga ka erasektori küberkaitse ettevõtete ja liitlastega, et tõsta USA kriitilise taristu ja seotud võrkude turvalisust.»
USA Hunt Forward meeskonnad mängivad väga olulist rolli USA küberväejuhatuse «Persistent Engagement» initsiatiivis, mille eesmärk on takistada pahatahtlikku tegevust küberruumis, mis jääb allapoole otsese sõjategevuse piiri. USA küberväejuhatuse ekspertide ülesanne on kaitsta USA valitsuse võrke ja platvorme vastaste eest.
USA relvajõudude nn. Defend Forward strateegia näeb ette koostööd oluliste partneritega, et ennetada küberruumis tegevusi, mida on võimalik kasutada ka USA kriitilise taristu vastu.
«Eesti digitaalne ühiskond sõltub küberist, samuti ka riigikaitse. Meie jaoks on oluline, et Eesti oli üks esimesi, kellega USA sellise ühisoperatsiooni läbi viis, mis andis meile võimaluse saada hinnang meie võrkude turvalisuse kohta. Kuivõrd oleme maailmas liidrid küberteemadel, siis peame olema valmis kogemusi jagama ka liitlastega, et oma võrke paremini kaitsta,» ütles Eesti kaitseministeeriumi asekantsler Margus Matt, kelle vastutusalasse kuulub ka küberpoliitika.
Potentsiaalseid ohte küberruumis hinnates annab selline partnerlus Eesti ja USA vahel võimaluse mõlemale riigile arendada enda küberkaitse võimeid, mis toetavad ka globaalset küberturvalisust. Pahavara tuvastamine ja selle kohta info jagamine avaliku ja erasektori osapooltega tõstab kõikide kasutajate turvalisust küberruumis.
«Küber on meeskonnasport – keegi ei suuda küberohte peatada üksinda,» ütles USA abikaitseminstri asetäitja küberpoliitika alal Thomas Wingfield. «Meie strateegia põhineb koostööle liitlastega ja partneritega erasektoris, akadeemilistes asutustes ning rahvuslike ja kohalike valitsusetega, tagamaks, et meie küberruum on turvaline ja avatud ning mootor innovatsiooniks ja arenguks,» lisas Wingfield. USA küberväejuhatus koostöös USA Euroopa väejuhatuse ja NATO liitlastega töötavad ööpäevaringselt, et takistada pahatahtlikku tegevust küberruumis.
Eesti kaitseväe küberväejuhatuse peamine eesmärk on toetada kaitseministeeriumi valitsemisala küberruumis. Küberväejuhatus loodi 2018. aastal tugevdamaks Eesti küberkaitse võimekust ja seeläbi terve Eesti turvalisust.
Eesti ja USA vaheline küberkoostöö toimub mitmel erineval tasandil USA küberväejuhatuse, USA Euroopa väejuhatuse, Marlyandi rahvuskaardi ja USA õhuväe küberväe juhatusega.
https://www.crn.com/news/security/firee ... nds-reportEmergency Directive 21-01 calls on all federal civilian agencies to review their networks for indicators of compromise and disconnect or power down SolarWinds Orion products immediately.
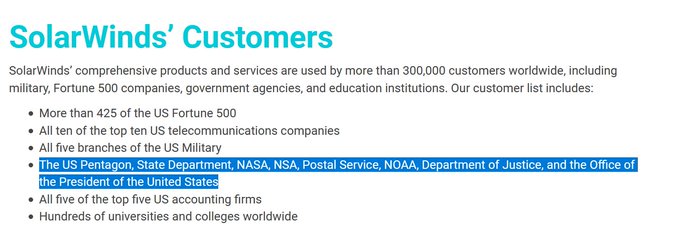
IT infrastructure mangement vendor SolarWinds disclosed Sunday that it experienced a highly sophisticated, manual supply chain attack on versions of its Orion network monitoring product released between March and June of this year.
https://breakingdefense.com/2020/12/con ... r-attacks/A classified assessment of America’s nuclear command, control and communications system (NC3) has rung alarm bells on Capitol Hill. The assessment was mentioned in a provision crafted by the Senate Armed Services Committee for the 2021 National Defense Authorization Act and accepted by the House in their conference deliberations.
https://mobile.reuters.com/article/amp/idUSKBN28R3BWMicrosoft was hacked as part of the suspected Russian campaign that has hit multiple U.S. government agencies by taking advantage of the widespread use of software from SolarWinds Corp, according to people familiar with the matter.
https://www.techdirt.com/articles/20201 ... XDz0mSidKUSecurity researcher Vinoth Kumar told Reuters that, last year, he alerted the company that anyone could access SolarWinds’ update server by using the password “solarwinds123”.
The known list of organizations that were hit by the SolarWinds supply chain attack include:
FireEye
U.S. Department of the Treasury
U.S. National Telecommunications and Information Administration (NTIA)
U.S. Department of State
The National Institutes of Health (NIH) (Part of the U.S. Department of Health)
U.S. Cybersecurity and Infrastructure Security Agency (CISA)
U.S. Department of Homeland Security (DHS)
U.S. Department of Energy (DOE)
U.S. National Nuclear Security Administration (NNSA)
Three US states (Specific states are undisclosed)
Microsoft
https://twitter.com/balticjam/status/13 ... 7011513346”The President-elect and his team are preparing a "cost imposition strategy"to respond to Russia -- not just for the hack,if Moscow is responsible, but for Russia's other disruptive actions also -measures that will include but won't be limited to sanct...”
https://www.bbc.com/news/world-us-canada-55989843Hacker tries to poison water supply of Florida city
Kasutajad foorumit lugemas: Registreeritud kasutajaid pole ja 5 külalist